Yesterday I had to export a certificate from an intranet portal using IIS 6.0 to Apache 2.2 running on Ubuntu server 10.4. even though there is plenty of information on the web how export a certificate from IIS to Apache, I think most of the information out of there is either not very clear or is incomplete.
On this post I hope to document the process of exporting a certificate from IIS to Apache as clear and complete as possible for those newbies like me doing this process for the first time.
Exporting The Certificate From IIS 6.0
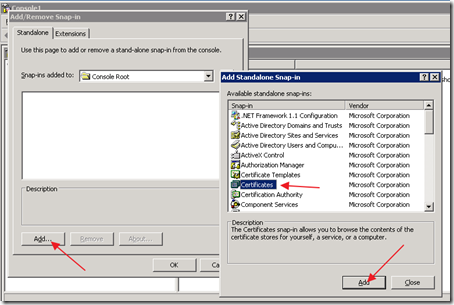
Login to your IIS server ( Windows Server ) and go to the RUN command and type “mmc” and click OK.. the MMC management console will come up. on the console click on File and then Add/Remove Snap-in then click on Add and then choose Certificates from the snap-in list and click on Add again:
Select Computer account on the following window, and then click on Finish. click on close in the rest of the windows you have open. then on your Certificates tree under the Personal folder click on Certificates. you should see the certificates on the right hand side. Right-click on the certificate you want to export and choose All Tasks and then Export:
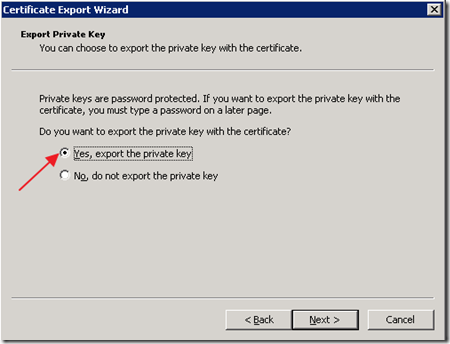
the Certificate Export Wizard will come up. click on Next. on the following window make sure you select “Yes, export the private key”
click on Next, choose Personal Information Exchange –PKCS #12 (.PFX) on the following window, and then enter a password for your certificate on the following screen. save the file in the following screen. preferably you should name the file the same as the domain you’re exporting. for example I called my certificate forevergeeks.com click on Finish on the last screen, and you should be done exporting the cert.
Importing The Certificate To Apache
upload the exported .PFX file to your Apache web server. I’m putting my file at the /var directory. it does not matter in what directory you put your file, just make sure you know the path of that directory. once the certificate is uploaded to the server establish a SSH console connection to the server so you can run some commands. I use putty.exe for this.
you also will need openSSL to execute these commands. type Sudo apt-get openssl if if openSSL is not installed on your server. then, the first thing we will do is to export the private key from the .PFX file. to do that, type this command in terminal:
openssl pkcs12 -in filename.pfx -nocerts -out key.pem
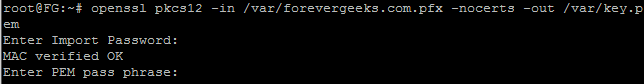
for example, my file is on the “var” directory on the apache web server, so I type “openssl pkcs12 –in /var/forevergeeks.com.pfx -nocerts –out /var/key.pem”
you will be asked for the import password. this is the password you entered when exporting the certificate. then the command will ask you for a MAC password, and verify it.
Next we will need to export the certificate from the .pfx file. to do that, execute the following command:
openssl pkcs12 -in filename.pfx -clcerts -nokeys -out cert.pem
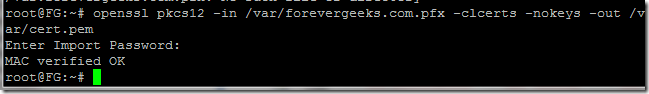
again, substitute the filename.pfx with your file name. for example, I’ll type “openssl pkcs12 –in /var.forevergeeks.com.pfx -clcerts -nokeys –out /var/cert.pem”
Now we need to remove the passphrase from the private key, so the web server does not ask for it every time it starts. to do that execute the following command:
openssl rsa -in key.pem -out server.key
again, you need to pay attention to the path where your files are. for example, my key.pem file is in the /var directory in my web server. so that command for me will be openssl rsa –in /var/key.pem –out /var/server.key
that’s it, you are done importing the certificate. now you need to make your web server recognize the certificate so when people go to your site using SSL they get a green URL instead of the certificate warning saying the certificate is not valid.
to enable the SSL functionality on your apache web server, type the following command:
sudo a2ensite default.ssl
hence that command is to enable the default.ssl file on your apache server. if you already have a virtualhost file please substitute this name with yours.
now using your FTP client open the default.ssl file located at /etc/apache2/sites-available folder, and add the following lines:
SSLEngine on
SSLCertificateFile /path/to/certificate/cert.pem
SSLCertificateKeyFile /patch/to/key/server.key
in my example that will look like this:
SSLEngine on
SSLCertificateFile /var/cert.pem
SSLCertificateKeyFile /var/server.key
save the file and restart your apache server with the following command:”
sudo /etc/init.d/apache2 restart
your certificate should be working now! that’s it, you’re done.
Was this article helpful?
Your feedback helps us improve our content.
0 people found this helpful!